0x0: mov rdi, 0x80cd40
0x0: mov esi, 0x80b348
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd41
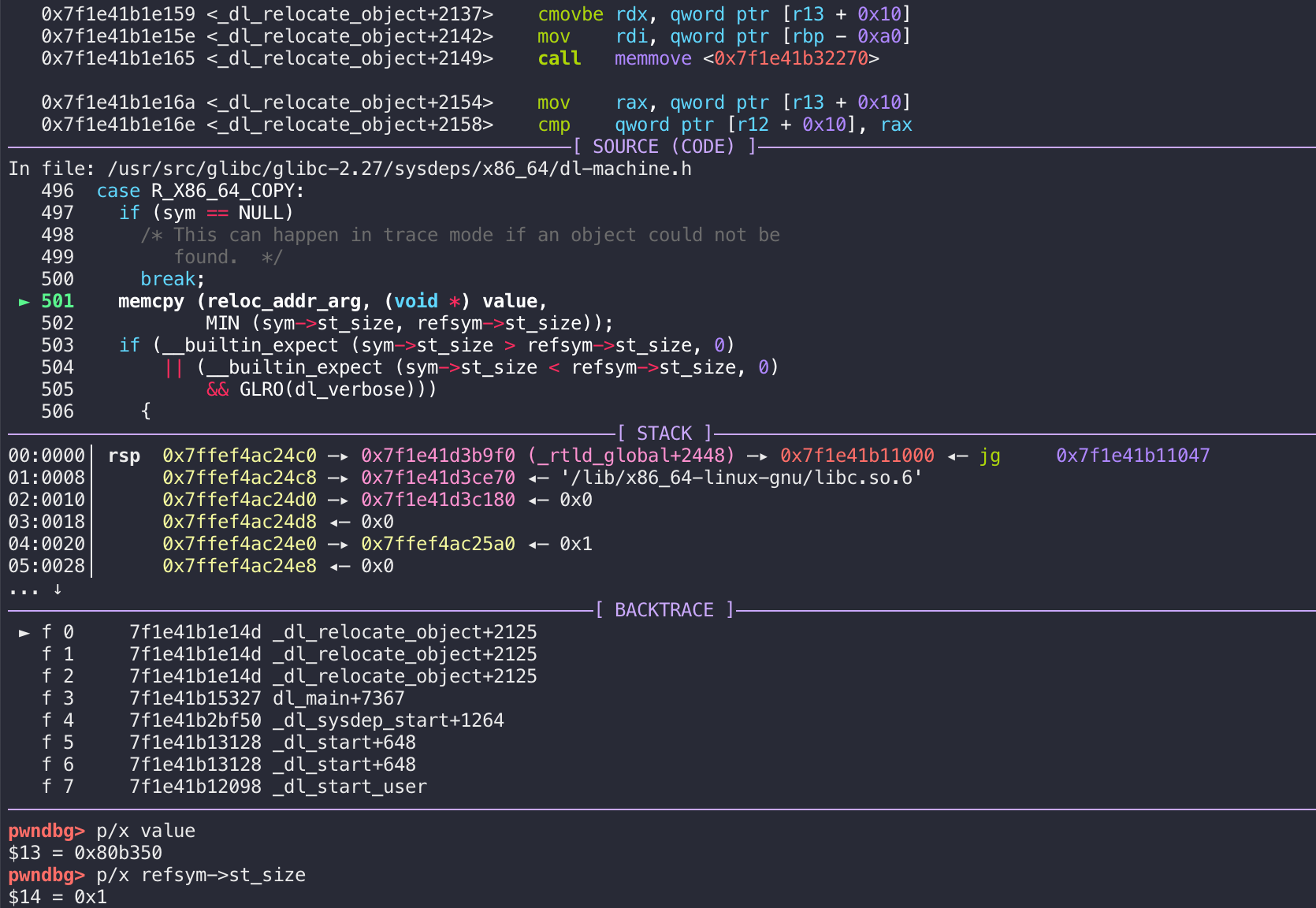
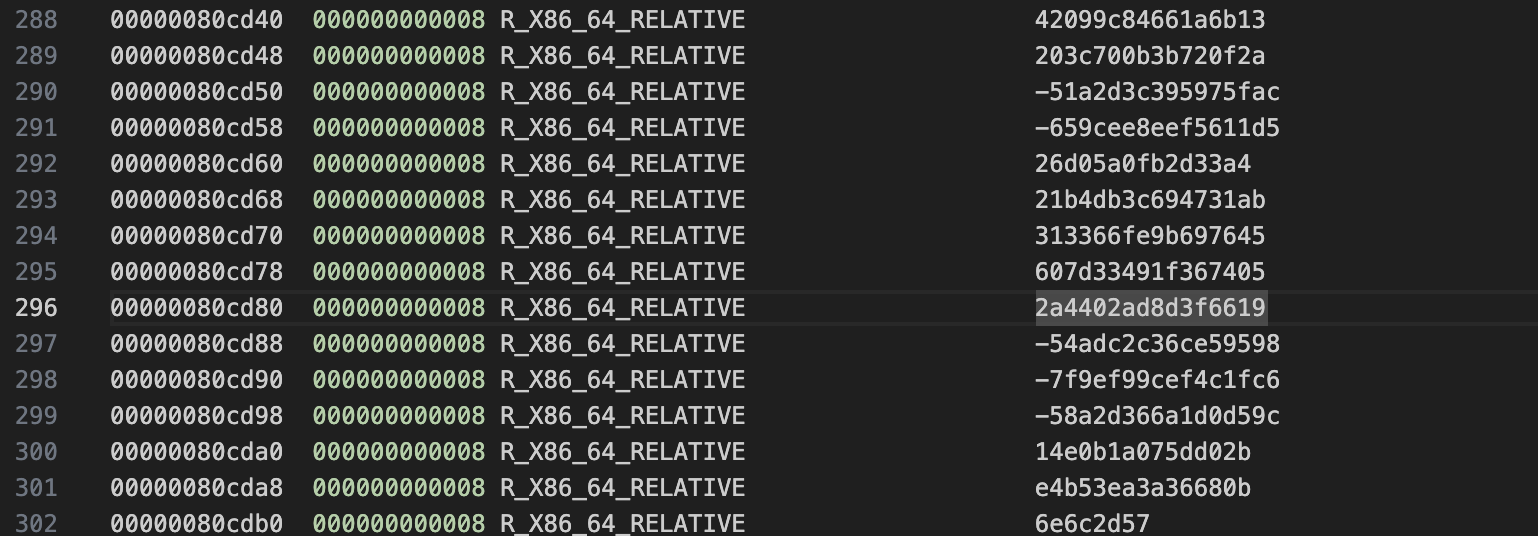
0x0: mov esi, 0x80b350
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd42
0x0: mov esi, 0x80b358
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd43
0x0: mov esi, 0x80b360
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd44
0x0: mov esi, 0x80b368
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd45
0x0: mov esi, 0x80b370
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd46
0x0: mov esi, 0x80b378
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd47
0x0: mov esi, 0x80b380
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd48
0x0: mov esi, 0x80b388
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd49
0x0: mov esi, 0x80b390
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd4a
0x0: mov esi, 0x80b398
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd4b
0x0: mov esi, 0x80b3a0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd4c
0x0: mov esi, 0x80b3a8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd4d
0x0: mov esi, 0x80b3b0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd4e
0x0: mov esi, 0x80b3b8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd4f
0x0: mov esi, 0x80b3c0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd50
0x0: mov esi, 0x80b3c8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd51
0x0: mov esi, 0x80b3d0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd52
0x0: mov esi, 0x80b348
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd53
0x0: mov esi, 0x80b350
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd54
0x0: mov esi, 0x80b358
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd55
0x0: mov esi, 0x80b360
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd56
0x0: mov esi, 0x80b368
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd57
0x0: mov esi, 0x80b370
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd58
0x0: mov esi, 0x80b378
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd59
0x0: mov esi, 0x80b380
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd5a
0x0: mov esi, 0x80b388
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd5b
0x0: mov esi, 0x80b390
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd5c
0x0: mov esi, 0x80b398
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd5d
0x0: mov esi, 0x80b3a0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd5e
0x0: mov esi, 0x80b3a8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd5f
0x0: mov esi, 0x80b3b0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd60
0x0: mov esi, 0x80b3b8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd61
0x0: mov esi, 0x80b3c0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd62
0x0: mov esi, 0x80b3c8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd63
0x0: mov esi, 0x80b3d0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd64
0x0: mov esi, 0x80b348
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd65
0x0: mov esi, 0x80b350
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd66
0x0: mov esi, 0x80b358
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd67
0x0: mov esi, 0x80b360
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd68
0x0: mov esi, 0x80b368
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd69
0x0: mov esi, 0x80b370
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd6a
0x0: mov esi, 0x80b378
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd6b
0x0: mov esi, 0x80b380
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd6c
0x0: mov esi, 0x80b388
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd6d
0x0: mov esi, 0x80b390
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd6e
0x0: mov esi, 0x80b398
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd6f
0x0: mov esi, 0x80b3a0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd70
0x0: mov esi, 0x80b3a8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd71
0x0: mov esi, 0x80b3b0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd72
0x0: mov esi, 0x80b3b8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd73
0x0: mov esi, 0x80b3c0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd74
0x0: mov esi, 0x80b3c8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd75
0x0: mov esi, 0x80b3d0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd76
0x0: mov esi, 0x80b348
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd77
0x0: mov esi, 0x80b350
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd78
0x0: mov esi, 0x80b358
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd79
0x0: mov esi, 0x80b360
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd7a
0x0: mov esi, 0x80b368
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd7b
0x0: mov esi, 0x80b370
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd7c
0x0: mov esi, 0x80b378
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd7d
0x0: mov esi, 0x80b380
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd7e
0x0: mov esi, 0x80b388
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd7f
0x0: mov esi, 0x80b390
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd80
0x0: mov esi, 0x80b398
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd81
0x0: mov esi, 0x80b3a0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd82
0x0: mov esi, 0x80b3a8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd83
0x0: mov esi, 0x80b3b0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd84
0x0: mov esi, 0x80b3b8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd85
0x0: mov esi, 0x80b3c0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd86
0x0: mov esi, 0x80b3c8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd87
0x0: mov esi, 0x80b3d0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd88
0x0: mov esi, 0x80b348
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd89
0x0: mov esi, 0x80b350
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd8a
0x0: mov esi, 0x80b358
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd8b
0x0: mov esi, 0x80b360
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd8c
0x0: mov esi, 0x80b368
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd8d
0x0: mov esi, 0x80b370
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd8e
0x0: mov esi, 0x80b378
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd8f
0x0: mov esi, 0x80b380
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd90
0x0: mov esi, 0x80b388
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd91
0x0: mov esi, 0x80b390
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd92
0x0: mov esi, 0x80b398
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd93
0x0: mov esi, 0x80b3a0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd94
0x0: mov esi, 0x80b3a8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd95
0x0: mov esi, 0x80b3b0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd96
0x0: mov esi, 0x80b3b8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd97
0x0: mov esi, 0x80b3c0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd98
0x0: mov esi, 0x80b3c8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd99
0x0: mov esi, 0x80b3d0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd9a
0x0: mov esi, 0x80b348
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd9b
0x0: mov esi, 0x80b350
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd9c
0x0: mov esi, 0x80b358
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd9d
0x0: mov esi, 0x80b360
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd9e
0x0: mov esi, 0x80b368
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cd9f
0x0: mov esi, 0x80b370
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda0
0x0: mov esi, 0x80b378
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda1
0x0: mov esi, 0x80b380
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda2
0x0: mov esi, 0x80b388
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda3
0x0: mov esi, 0x80b390
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda4
0x0: mov esi, 0x80b398
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda5
0x0: mov esi, 0x80b3a0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda6
0x0: mov esi, 0x80b3a8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda7
0x0: mov esi, 0x80b3b0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda8
0x0: mov esi, 0x80b3b8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cda9
0x0: mov esi, 0x80b3c0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdaa
0x0: mov esi, 0x80b3c8
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdab
0x0: mov esi, 0x80b3d0
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdac
0x0: mov esi, 0x80b348
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdad
0x0: mov esi, 0x80b350
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdae
0x0: mov esi, 0x80b358
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdaf
0x0: mov esi, 0x80b360
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdb0
0x0: mov esi, 0x80b368
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdb1
0x0: mov esi, 0x80b370
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdb2
0x0: mov esi, 0x80b378
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
0x0: mov rdi, 0x80cdb3
0x0: mov esi, 0x80b380
0x6: mov al, byte ptr [rdi]
0x0: xor al, byte ptr [rsi]
0x2: mov byte ptr [rdi], al
0x4: ret
|